Momentarily I am recovering from a bad flu, which kept me from doing work for more than week, and I came across some interesting notes from myself and some colleagues from Inter Access. These notes were written during LEAP 2008 at Kim Cameron’s session “Digital Identity – Why claims will Change Everything”, Clemens Vasters session “Internet Service Bus Overview” and Norm Judah’s talk about “The last architectural mile”. I was thinking of sharing them with you blog readers, so here they are.
Digital Identity – Why claims will Change Everything
Kim Cameron, Architect of Identity, Microsoft
In this session about Digital Identity Kim showed his vision in the (near) future on identities, authorization and authentication: Claims Based Authentication. After describing problems with current mechanisms for establishing identity, authorizations and authentication he gave an overview on developments in the area of claims based authentication. His session ended with an demo of CardSpace and a Mac variant DigitalMe.
What is a claim? A claim is more or less an collection of related attributes that enables a service if and how it should present itself to a caller. These claims comply to seven laws of digital identity:
1. User Control and Consent: Digital identity systems must only reveal information identifying a user with the user’s consent.
2. Limited Disclosure for Limited Use: The solution which discloses the least identifying information and best limits its use is the most stable, long-term solution.
3. The Law of Fewest Parties: Digital identity systems must limit disclosure of identifying information to parties having a necessary and justifiable place in a given identity relationship.
4. Directed Identity: A universal identity meta system must support both “omnidirectional” identifiers for use by public entities and “unidirectional” identifiers for private entities, thus facilitating discovery while preventing unnecessary release of correlation handles.
5. Pluralism of Operators and Technologies: A universal identity meta system must channel and enable the interworking of multiple identity technologies run by multiple identity providers.
6. Human Integration: A unifying identity meta system must define the human user as a component integrated through protected and unambiguous human-machine communications.
7. Consistent Experience Across Contexts: A unifying identity meta system must provide a simple consistent experience while enabling separation of contexts through multiple operators and technologies.
An example how Claim Based Authentication works is as follows:
A user (or applications) call a service. Service provider on its turn determines what the user has to comply too to be able to call the service. User calls an identity provider (i.e. directory service) a security token (claim) that gives him/her the authority to call the service. This token does not contain more information than necessary. This token is then presented to the service provider and on basis of this (identified through a trusted party : identity provider) the user is granted access to the service. This shows that there is no strong coupling between a service and party delivering the token, trust is sufficient. Also no more information is passed than strictly necessary and privacy of the user is guaranteed.
Internet Service Bus Overview
Clemens Vasters, Senior Program Manager, Connected Systems Division
‘BizTalk Services’ is the codename for concept ‘Internet Service Bus’. BizTalk Services are not the same as BizTalk Server, although one could think because of the naming that they are. No BizTalk Services are an implementation of Enterprise Service Bus (ESB) technology, were services do not have to be present locally at an customer, but could be hosted elsewhere for instance Microsoft, one of her partners or hosting company. Hosting services becomes flexible this way and moving them from locally to a third party or vice versa is easy. BizTalk Service are a part of the so called software plus services concept: new mantra of Microsoft where services like Microsoft Office, Exchange, BizTalk and so on are offered on the internet (or cloud) or through third parties or locally inside the organization (on-premise versus off-premise).
In a nutshell concept of Internet Service Bus is as follows:
This architecture brings the following possibilities:
• Simple publish and subscribe event model
• A globally addressable name for services
• Able to safely provide services behind a firewall or NAT
• Support for multiple listeners and senders on one URI (multicast)
• If desirable: automatic and transparent buildup of connections between endpoints instead of routing through internet service bus
The last architectural mile
Norm Judah, CTO Microsoft Services
Science, art and balance
Architecture as a mix of science, art and balance: fresh new approach of looking at architecture. Science as identifying and understanding the proper choices to be made and aspects inside architecture, art as in naked essence of simplifying matters and balance in finding the balance between science and art. Question asked during this session was: which choices have to be made to see that technology will be future proof? What to invest in or not? A lot aspects play a role here: aim for IPv6 or just go on with wireless protocols, platform choices, service abstraction layers, business rules, which devices, identity management…
Topics and trends
Norm sees some new trends like:
• Power to the edge
• End user adoption
• Engineered for health
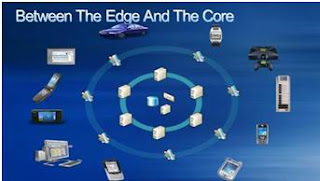
Power to the edge is the service abstraction layer: investments in current systems can exist with possibility to offer services through Line-Of Business or other systems to consumers and devices.
In the picture above functions of systems are surrounded by services (service abstraction layer). By decoupling functions they can be placed in an “outer ring” that can provide functionality to consumers/devices; data integrity, business rules etcetera are in the middle and inside the systems. Necessity to change IT landscape is delivering support of people in a broader context than usually, which is called in MS terms: always on, always connected. A world where people determine how they work, when they work and with whom they work (see also New World of Work).
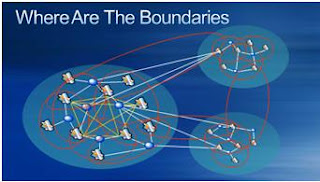
This change will have impact, because how will the world look where organizations split itself into services, and who will use each other services and how will inter-organizational collaboration start? Where does begin and where does ones responsibility end, who owns what and who determines who can do what with who? His presentation did not answer these questions.
Technorati:![]() LEAP 2008
LEAP 2008